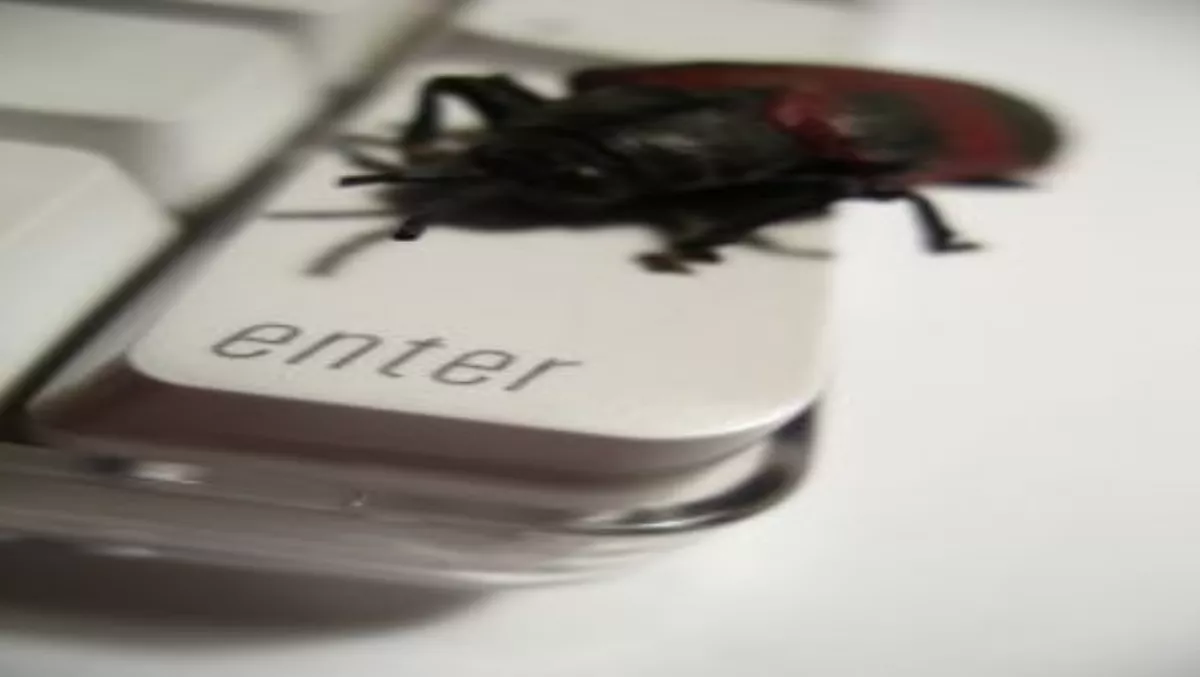
Botnets were the leading online security problem for 2009, and they’ll be smarter next year, to make it harder to take them down.That’s the key conclusion from the MessageLabs Intelligence 2009 Security Report, just released.It says the ten major heavyweight spam-sending botnets, including Cutwail, Rustock and Mega-D, now control at least five million compromised computers. Cutwail was a dominating force across both spam and malware in 2009, responsible for issuing 29% of all spam or 8500 billion spam messages between April and November 2009. Cutwail also used its strength to spam out emails containing the Bredolab Trojan dropper, disguised in the form of a .ZIP file attachment.Bredolab was designed to give the sender complete control of the target computer which then could be used to deploy other botnet malware, adware or spyware onto the victim’s computer. The percentage of spam distributing the Bredolab Trojan dropper increased steadily in late 2009 and reached its highest levels in October 2009, when it was estimated that approximately 3.6 billion Bredolab malware emails were in circulation.In 2009, 90.6% of spam contained a URL, or hyperlink, which helped disguise the true Web site that the user would be visiting and making it harder for traditional anti-spam filters to identify the messages as spam. A growing trend noticed was the use of shortened URLs, which are frequently used on social networking and micro-blogging sites and are popular among online criminals because of the inherent trust relationships that exist between users of these sites. “With compromised computers issuing 83.4% of the 107 billion spam messages distributed globally per day on average, the shutdown of botnet-hosting ISPs, such as McColo in late 2008 and Real Host in August 2009 appeared to make botnets re-evaluate and enhance their command and control backup strategy to enable recovery to take hours, rather than weeks or months,” the report says. “It is predicted that in 2010 botnets will become more autonomous and intelligent, with each node containing an inbuilt self-sufficient coding in order to coordinate and extend its own survival.”Read the full report here. (Adobe Reader required)