PROTECT YOUR HOME NETWORK
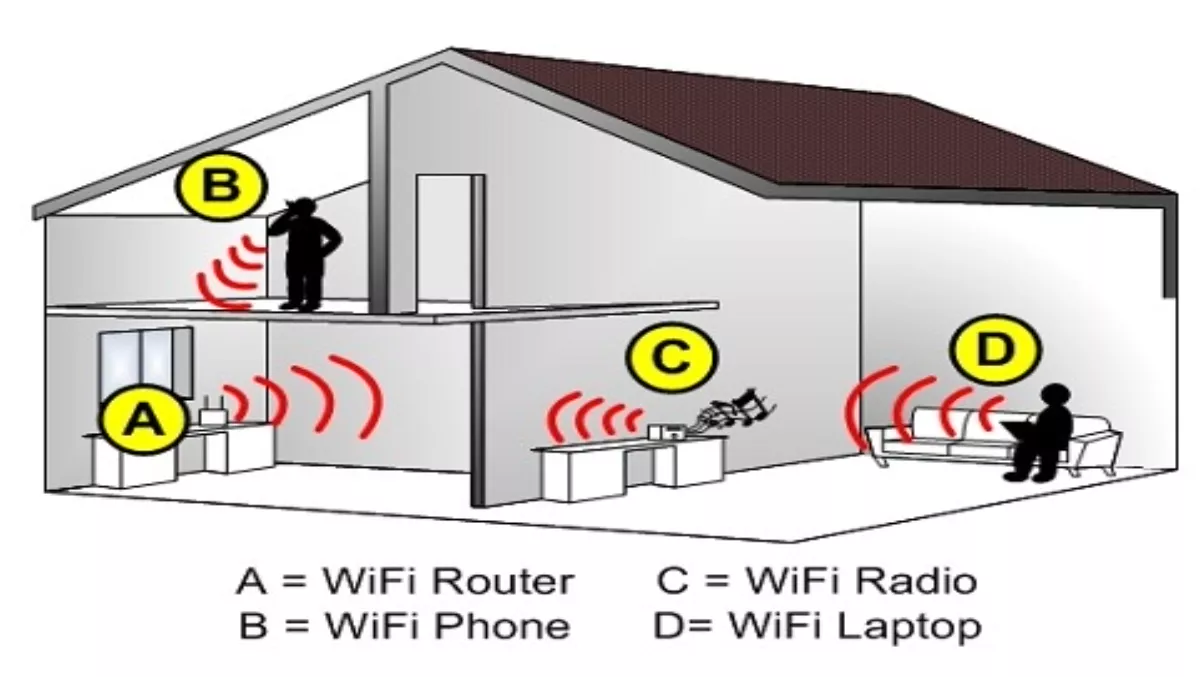
So you've set up your home network and are ready to begin surfing the web. Let's say for the purpose of this article that you've chosen the wireless route, as this is becoming increasingly popular and is also the type of network most likely to run into security threats.
A wireless network is great because it means that you can use all of the computers in your house online and you can move them around without losing connection. The downside is that it's nearly just as easy for cybercriminals to gain access to your wireless as it is for you. There are now millions of wireless home networks floating around, which you can see when you ask your computer to "view available wireless networks.” You can also see how easy it is to access many of these networks that are left insecure, and if you are one of them this means that your neighbours can see what you are doing online.
Although there is a lot of talk about the safety of wireless, most of the time when people run into problems it is due to a lack of knowledge and the fact that they have unknowingly left their network open and unprotected. Frank Hanzlik, managing director of the Wi-Fi Alliance noted that a "good percentage of wireless users have simply not turned on their wireless security.
You are always going to be taking a small risk when you use a wireless network, but in this article, we offer you some ways to reduce that risk and protect your home network from hackers.
First of all, turn off the broadcast SSID function, making it harder for people to find your wireless network to begin with. The SSID (Service Set Identifier) is the name that anyone who wants to access the line must know, and most of the time, it is automatically turned on, broadcasting your network to the public to make it easier to connect. By simply turning this off, you have taken a huge step towards securing your network.
After turning off the SSID function, you should change the name of your network. Don't use the default name that came with the device, as this is easy for hackers to guess. We recommend changing your SSID every few months, much like you would change a password.
Another way to keep yourself protected, which many people don't know about it, is encryption. Most wireless devices today come with a new and improved encryption tool called Wi-Fi Protected Access (WPA) and now WPA2, which is considerably stronger than what we used to see with WEP when wireless first arrived on the scene. However, if you don't know to activate this feature, then it's not going to do you a lot of good! Make sure you enable encryption: at least this way, even if someone manages to get onto your network, they won't be able to see what you're doing unless they have access to special hacking tools.
Finally, be sure to set a password for your wireless network. Read the user's manual that came with your router for instructions on how to do this. Choose a password made up of a random sequence of characters, mixing lowercase, uppercase and numbers. Additionally, try to make your password the maximum length of characters allowed. Although this might be tougher for you to remember, it is also much tougher for hackers to guess, so it's really worth the extra effort.
Another step you can take (but it is only available on some wireless devices) is to enable MAC address filtering on your access point or router. A MAC (no, we're not talking about the computer model!) address is a code unique to every computer device with networking capabilities. MAC address filtering will register the hardware MAC address of your networked devices, only allowing those specific devices to access the network. Although hackers can clone your MAC addresses, it just adds another barrier of safety between them and your network.
Read part three here.